COMP 4108 Assignment 5
Due 11:59PM on April 10
Assignment out of 48 marks total
Submission Requirements:
For this assignment you will work individually.
You should submit the following TWO files:
- A PDF of your assignment report, including a cover page with the assignment details and your name with student number.
- A tar or zip file (yes, even if there is only a signle file included) containing any code or scripts that you wrote. Any included files must be referenced in the PDF report, else they will not be reviewed. See the General Page for instructions on how to create a tar file.
For each question, include the following (where applicable or otherwise unspecified):
- What you did (i.e., your answer to the question -- e.g., a command, action on a webpage, code run, etc.).
- How you did it (i.e., the exact command you ran to find the answer or complete an action if required -- e.g., Linux command line, area on a website that you went to, configuration, etc.).
- Your explanation of what you did and why you did it.
- The output or result of what you did, trimmed to include only the relevant output (i.e., cut out previous commands' text, un-needed text, etc.). This is often in the form of a screenshot.
Note that, depending on the question, some of the above requirements will not necessarily exist. Also, #1 and #2 from above can often be combined into a single screencap. Also note that some questions may explicitly state what to submit. This is to ensure you submit the correct information we're looking for, and the other requirements are expected as well (see list above).
These requirements may seem tedious and unnecessary; however, they are useful for markers to see that you completed each question, explained that you understood the question, and provided proof that the task was successfully completed.
When in doubt, explain as much as you can. I need to see that you understand the answer and the process you used to get the answer. Not including an explanation or providing too little explanation may result in lost marks.
Any code or scripts included in the tar archive is for the TA to test, and should therefore be submitted in a format that is easy to run/compile, e.g., with an appropriate directory structure (if needed), required Makefiles, etc.
Code that you include in your report is for the TA to read, and may therefore be formatted to best explain what you did, e.g., by sectioning the code, highlighting lines of interest and including additional comments, etc.
SUBMITTING CODE WITHOUT EXPLANATION WILL RESULT IN SEVERE PENALTY!
Instructions on how to copy files to and from your local machine and your VM are available on the General page. You may find this useful for submitting code/scripts/log files/etc.
Introduction
Port Scanning
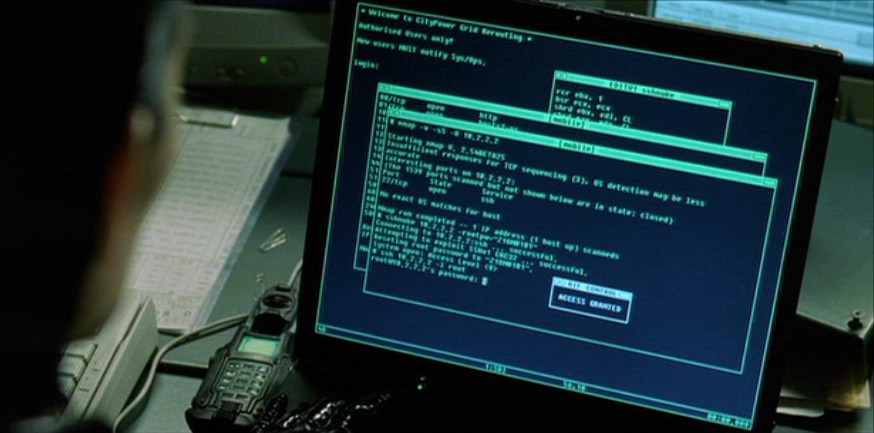
Conquest requires exploration, and for our purposes we're going to focus on port scanning. Port scanning allows an administrator (or an adversary) to probe a machine on the network in order to locate services the machine offers. Far from just determining if a port is open or closed the network reconnaissance tool we are going to use (nmap) is capable of numerous scan types, OS and service fingerprinting, and supports advanced scripting. The nmap project is so well known it has even had cameo appearance in several movies (including the Matrix). Whole books have been written on nmap, we are going to cover only a small subset of the core features.Lest you get misidentified as a script kiddie it's important you learn not only how to use nmap, but what the various scans are doing. A great way to do that is by diving into a system administrator's two best friends:
netcat and tcpdump.
Netcat acts as a networking swiss army knife, allowing you to quickly erect and destroy TCP and UDP servers/clients. In keeping with the tenets of the UNIX philosophy netcat is a simple tool that acts as a filter, allowing you to pipe commands and files to/from network sockets. The TCP Dump command allows you to record traffic from network adapters in a raw form suitable for process by other tools. TCP Dump is invaluable for sniffing traffic and debugging network applications. You might find reading a quick primer on tcpdump helpful if you have not used it before.
Firewalls
Since you're getting so comfortable on your freshly rooted VM it might be time to fortify the defenses. You never know when someone with better exploits will stumble onto your hide-away.A classic way a system administrator will lock down a machine, or network is by utilizing a firewall. The Linux Kernel supports a Firewall through the use of
iptables. When wielded by the right user the iptables framework allows for sophisticated firewall rules to be crafted. We will be just scratching the surface of what iptables allows in the second part of the assignment.The iptables man page and the Ubuntu IP Tables How To have enough information to get you started. It might also be helpful to read some example rules, and their explanations. An important thing to remember when learning iptables is that there are no confirmation messages, or logic to prevent you from doing something silly unintentionally. Without great care you can easily block all network access to the machine. This can be especially problematic when you are remotely administering the machine OVER the network you just blocked.
It is also worth stressing that the order that rules appear in the tables is very important! A best practice is to define your firewall in a bash script. At the beginning of the bash script you can drop all existing rules (see
man iptables for how), then add each rule in the correct order from the script. This approach has many benefits:
- Applying all of the rules with one command
- Applying them in a fixed order to a known (i.e. empty) state
- Allowing ample time to triple check you wrote the rules correctly before running them
Please do not use UFW, or any other layer on top of iptables to complete your assignment. While sometimes easier to use, these solutions are not as portable. Vanilla iptables are available on everything from a tiny Raspberry PI device to 64 CPU super computing clusters, regardless of Linux distro.
Dummy Services
On your VM a set of dummy network services has been installed. These services listen on randomly chosen ports between 10000 and 20000. The port numbers differ from one student VM to the next, but remain constant between VM reboots. Each dummy service merely listens for one line of text over a TCP connection and replies with a translation of the input line.For the first portion of the assignment you will be scanning your own VM to find these services using
nmap, interacting with the services using netcat and observing traffic to/from your VM and the services using tcpdump
The second portion of the assignment will have you building a firewall using iptables to shield the dummy services.
Inadvertent Lockouts
While writing your firewall rules in Part B, you may inadvertently firewall yourself off from your VM, breaking your SSH connectivity. Thankfully, in the event that you block yourself from accessing your VM, or otherwise get the firewall into an unknown state, you may access your VM console from the OpenStack web interface and clear the offending firewall rule.
Also note that iptables rules are cleared on each reboot. Normally a system administrator would ensure the firewall is recreated on each machine boot, but we have skipped this step to facilitate testing.
Part A - Nmap & TCP dump - 24 marks
- 2 Marks - Using
nmap, perform aTCP SYNscan on yourlocalhostto find all of the open TCP ports. Ensure that you exhaustively check all ports and not the just most popular services. Submit both the nmap command you ran as well as the output produced.
Hint:
Thenmapcommand is incredibly versatile, offering a plethora of configuration options. Most of these settings have a default that is optimized for the more common scan scenarios. Be sure to read the nmap man page to learn what some of these defaults are. - 4 Marks - Create a single line text file called
input.txtcontaining a sentence of English. Using thenetcatcommand send input.txt over the network to each of the open ports you found in Q1. For full marks, write a bash function or script that processes the output ofnmapand usesnetcatto transmit input.txt to each of the open ports automatically. Submit your input.txt file, any commands you enter, any scripts you write, and a copy of the output generated.
Hint:
A quick and dirty approach would be to use the many text manipulation tools available in a bash environment (head,tail,cut,sed,awkand so on) to process the nmap output.
A better option is to use nmap's XML output mode and the same text processing tools, or a scripting language such as Python. - 2 Marks - Using the
tcpdumpcommand, create an expression to match TCP packets that meet the following criteria:- Are received on any interface.
- Have a destination port equal to one of the services from Question 1. Choose one of the services you were able to find/interact with.
Verify that your tcpdump command works by connecting to the port you specified usingnetcatand transmitting your input file. Submit both your tcpdump command expression as well as the output generated by tcpdump when you connect with netcat. - 2 Marks - Modify the
tcpdumpcommand that you created for the previous question such that it prints the link-layer headers and data of the packet in hex format, and outputs to a file. Submit both the tcpdump expression as well as an output file created when you test the expression. - 4 Marks - Run both a
nmapTCP FINscan as well as aTCP ACKscan onlocalhost. Capture both incoming and outgoing packets from both scans to a file usingtcpdump. Using excerpts from the capture file, explain the difference between theTCP FINandTCP ACKscans. Submit the commands you used to run the scans, the command you used to capture the packets, and your explanation of what information these scans capture (i.e., when/why would you use them) and how they glean this information. - 4 Marks - Run both a
nmapTCP connect()and aTCP SYNscan onlocalhost. Capture both incoming and outgoing packets from both scans to a file usingtcpdump. Using excerpts from the capture file, explain the difference between theTCP connect()andTCP SYNscans. Submit the commands you used to run the scans, the command you used to capture the packets, and your explanation of what information these scans capture (i.e., when/why would you use them) and how they glean this information. - Run an
nmapdiscovery scan on all hosts on the192.168.18.0/23network. Make sure you only perform a discovery scan and not a port scan. When scanning a large block of hosts it often makes sense to find which hosts are online using a discovery scan and then following up later with a port scan.- 2 Marks - Submit both the nmap command you ran as well as the output generated.
- 1 Mark - Describe the hosts that you've found, i.e., what do you think they are, and why?
- 2 Marks - Pick one of the hosts you discovered, and use the
nmapOS Detection feature to attempt identification of the OS that it is running. Submit the command that you ran and the output generated (use the verbose flag). Do the results confirm your hypothesis from (b)? Explain why or why not, along with any potential reasons.Note:Use
sudofor the discovery scan and OS detection function. Without it, you'll get an incomplete list of hosts.
- 1 Mark -
tcpdumpis a useful tool for implementing which security principle mentioned in Chapter 7 of the course textbook? Give the principle name, number, and a brief description of how it is relevant totcpdump.
Part B - IP Tables Firewall - 24 Marks
-
1 Mark - List the active rules in the
INPUT,OUTPUT, andFORWARDchains of iptables from your VM before you have added any rules. Submit the command you ran as well as the output. -
8 Marks - Write a firewall script that when run, does the following:
- Zeroes the iptables counters
-
Adds a rule for the
INPUTchain that drops all packets with an invalid state. - Adds a rule for the
INPUTchain to allow packets with statesESTABLISHEDorRELATEDto be accepted. -
Adds a rule for the
INPUTchain that allows TCP packets with the syn flag set, destined for port 22, in theNEWstate to be accepted. -
Adds a rule for the
INPUTchain that accepts ICMP packets with typeecho-requestto be accepted. -
Adds a rule for the
INPUTchain that rejects all packets that do not meet any of the above rules.
Submit the firewall script file in its entirety.
Hint:
Order matters! The order of the rules in your script should adhere to the ordering of the questions.
Hint:
The firewall script does not have to be a complex script. Most often an iptables script is just an easy way to run a handful of staticiptablescommands at once. The advanced features of bash can be introduced as required. Using bash allows for anything from keeping commonly referenced IP addresses or ports in a variable to accepting command line arguments, resolving hostnames, or looking up system information as required.- 3 Marks - Run your firewall script to apply the rules. Verify the rules are working by opening a new SSH connection into your machine and running your nmap scan from Part A, Q1. Also try connecting to some of the services you found in Part A, Q1 using netcat. Capture both incoming and outgoing packets from the scan to a file using
tcpdump. Submit the list of active firewall rules (including their counter values) as generated byiptables-save, as well as the results of your nmap scan.
Hint:
Each iptable rule keeps a counter of the number of packets that it matched. This behavior can be very useful when debugging new firewall rules, or verifying their behaviour.- 3 Marks - Modify the last rule in the
INPUTchain to drop all packets that do not meet any other rule. Again, run your nmap scan from Part A, Q1. Capture both incoming and outgoing packets from the scan to a file usingtcpdump. Compare the output of this packet capture with the one performed in the previous question. Using excerpts from the packet captures, describe the difference between the drop and reject behaviour.
Hint:
Make sure you flush your reject rule before adding the drop rule.- 4 Marks - Modify your firewall script to add a rule that accepts TCP packets that meet the following conditions:
- The syn flag is set
- The destination port is a service of your choice from Part A, Question 1.
- The connection is in the
NEWstate - The connection source address is local to your VM
- 3 Marks - Modify your firewall script to add a rule to drop outbound TCP connections to port 587. Flush your iptables rules, apply the modified script, and test that you can no longer telnet to
mail.ccsl.carleton.caon port 587 from your assigned VM. Submit the new firewall rule as well as the output from your testing.
Hint:
Thetelnetcommand is another quick way to test a network service. Feel free to usenetcatinstead oftelnet.- 2 Marks - When creating firewall rules it is important to keep in mind which security principle(s) from Chapter 7 of the course textbook? Give the name and number of the principle(s) and a brief explanation on why you chose the principle(s).