COMP 4108 Assignment 2
Due 11:59PM on Feb 14
Assignment out of 47 marks total
Submission Requirements:
For this assignment you will work individually.
You should submit the following TWO files:
- A PDF of your assignment report, including a cover page with the assignment details and your name with student number.
- A tar or zip file (yes, even if there is only a signle file included) containing any code or scripts that you wrote. Any included files must be referenced in the PDF report, else they will not be reviewed. See the General Page for instructions on how to create a tar file.
For each question, include the following (where applicable or otherwise unspecified):
- What you did (i.e., your answer to the question -- e.g., a command, action on a webpage, code run, etc.).
- How you did it (i.e., the exact command you ran to find the answer or complete an action if required -- e.g., Linux command line, area on a website that you went to, configuration, etc.).
- Your explanation of what you did and why you did it.
- The output or result of what you did, trimmed to include only the relevant output (i.e., cut out previous commands' text, un-needed text, etc.). This is often in the form of a screenshot.
Note that, depending on the question, some of the above requirements will not necessarily exist. Also, #1 and #2 from above can often be combined into a single screencap. Also note that some questions may explicitly state what to submit. This is to ensure you submit the correct information we're looking for, and the other requirements are expected as well (see list above).
These requirements may seem tedious and unnecessary; however, they are useful for markers to see that you completed each question, explained that you understood the question, and provided proof that the task was successfully completed.
When in doubt, explain as much as you can. I need to see that you understand the answer and the process you used to get the answer. Not including an explanation or providing too little explanation may result in lost marks.
johnsmith-assignment2.pdf
Any code included in the tar archive is for the TA to test, and should therefore be submitted in a format that is easy to run/compile, e.g., with an appropriate directory structure (if needed), required Makefiles, etc.
Code that you include in your report is for the TA to read, and may therefore be formatted to best explain what you did, e.g., by sectioning the code, highlighting lines of interest and including additional comments, etc.
SUBMITTING CODE WITHOUT EXPLANATION WILL RESULT IN SEVERE PENALTY!
Instructions on how to copy files to and from your local machine and your VM are available on the General page. You may find this useful for submitting code/scripts/log files/etc.
Introduction
This assignment will be done on the SCS OpenStack platform (please consult the General Page for further details and instructions). The name of the VM snapshot for this assignment is comp4108-w24-assignment-02. To protect your VM against abuse, you will automatically be prompted to choose a new password upon your first login—please do so, especially if you enable SSH access.
At the end of Assignment 1 you saw how you could exploit a setuid binary with a race condition in order to gain root privilege on the box. Now what? If you were a real attacker it could be a matter of minutes before the system admin patches the vulnerable program and gives you the boot. How do you hide your tracks? How do you install a backdoor that ensures you aren't a one-trick pony?
Familiarize yourself with the
history command. You can use it to refresh your memory on commands you may have entered.You may prefer to use the
script command, which records input and output to a file automatically. See man script for more information.
Linux Kernel Modules:
The answer to both questions (at least as far as this assignment is concerned) is a rootkit. A garden variety Linux rootkit is generally written as a Loadable Kernel Module or LKM. An LKM allow the system administrator to load new code to extend the kernel's functionality while the machine is running. Many device drivers are implemented as LKMs.
Only root can insert and remove modules (using insmod and rmmod respectfully), but it just so happens you're root today. Lucky you. There is a free guide to programming Linux Kernel Modules available online. This guide explains benign kernel module functionality, and you'll likely want to read (or at least skim) Sections 1, 2, 3, and 8.
This assignment assumes familiarity with the C programming language. If your C kung-fu is rusty you'll probably want to Google some reference material. The classic choice is the K&R book. The Carleton library has at least one copy. There's also Learn-C.org by Zed Shaw, available free online.
You'll want to make sure you understand pointers, memory management, arrays, and structures. You're a kernel programmer now.
Rootkits:
Rootkit LKMs alter the state of the system to present processes interacting with the Kernel sanitized information, or to add new functionality convenient for an attacker. A classic way this is done is by hooking system calls. For an idea of what system calls a process invokes, you should revisit your use of the strace command in Assignment #1. The guide to programming Linux Kernel Modules introduces syscall hooking briefly.
To hide files from appearing in directory listings for instance, you would find the syscall that ls used to get filesystem directory entries and hook it. By hooking syscalls related to the filesystem a malicious rootkit might hide all files with a $sys$ prefix, allowing it to stash its own files from the system. Rootkits also frequently serve as backdoors that allow a user to elevate their priviledges, or get a remote shell without logging in.
Back to the Future:
You no doubt saw the grave warnings affixed to both the getdents man page and the LKM guide section on hooking syscalls. Not only are these warnings correct, things are worse than you might imagine. These techniques are dangerous, and often unreliable. No sane engineer would design their device driver in this fashion, we're hacking in the true definition.
The details in the LKM guide are unfortunately specific to Linux Kernel versions < 2.6.x and a 32bit architecture. We're living in 2024 and running Linux Kernel version 5.4.x on a 64bit architecture. This affects us in two major ways:
- The
sys_call_tablesymbol is no longer exported by the kernel to LKMs. This is to prevent developers from doing stupid things with it. We're going to have to find the address manually so that we can do stupid things with it. - The page of memory where the
sys_call_tablelives is now marked read only to prevent things from going wrong. We can't write a new hook into the table without first making the page writable, thereby allowing things to go wrong.
Writing a rootkit from scratch is going to be a grueling endeavour. Thankfully your connections in the underground have hooked you up with some super eleet warez. With their C code you should be able to write a respectable piece of kernel malware without losing your mind. Unfortunately your hookup only got you so far. The code's author must have uploaded it before it was completely finished. It looks like you'll have to pick up where they left off...
Important Notes:
You're writing code that runs in kernel space, with full privileges. The slightest mistake in your code is going to lead to legitimately weird things happening including (but not limited to):
- All of the binaries on your system segfaulting. Including ssh.
- Data being lost.
- Kernel modules being stuck loaded.
- Full kernel panics, leaving the box frozen
Don't keep anything on your VM you aren't ready to lose! Keep your code on your own machine and copy it over to compile/test.
You're going to want to work in very small, verifiable steps. Do not attempt to sit down and program the whole assignment. Instead, start with very small steps in mind and progress further only when you get that step working.
For example, in the file hiding task: start by figuring out what to hook, then try hooking it and keeping the original behavior intact. Once you can do that without crashing your VM, try printing all filenames in a directory to syslog from your hook. Once that's working start writing code to identifying files you want to hide from those being printed to syslog. Finally attempt to remove the entry from the results.
Part A - Setup (7 marks)
When in doubt, read the source code! The Linux kernel is open source. The kernel installed on your VM is version 5.4. The corresponding source code is available in
/usr/src/linux-5.4.0-171.
- Download the rootkit framework code for this assignment, available here, to your VM using the
wgetcommand. THE USERNAME AND PASSWORD CAN BE FOUND IN A POST IN THE "Announcements" DIRECTORY ON BRIGHTSPACE. - Run
sudo bashto give yourself a bash shell with root privileges. We'll pretend that you got this from the race condition in A1. For most of this assignment you're going to be switching between a root user and a normal user, so I recommend you keep two windows open (the gurus might want to try the screen tool, or a terminal multiplexer with a somewhat steep learning curve). - 1 Mark Find the address of the
sys_call_tablesymbol inspecting/proc/kallsyms. - 0.5 Marks Edit the
rootkit.cfile to provide the right symbol as an argument tokallsyms_lookup_name()in theget_syscall_table_bf()function. It should the same as the symbol you found in Q3. - 0.5 Marks Confirm you can build the rootkit framework by running
make. You can safely ignore the warning about defined but not used variables, as you will be fixing that as you complete the assignment. - 0.5 Marks Confirm you can insert the rootkit module by running
./insert.shas root. Ensure it was inserted by runninglsmodand by checking the syslog. - 0.5 Marks Confirm you can remove the rootkit module by running
./eject.shas root. Ensure it was ejected by runninglsmodand by checking the syslog. - 2 Marks Finish the rootkit code so that the example
open()hook works. Look for the TODO markers. Show a snippet of the syslog output it generates once loaded. - 2 MarksChoose 2 principles from Chapter 1.7 of the course textbook and explain how they can help mitigate rookits. The way in which the principle helps could be with mitigating rootkit effectiveness or delivery. Please clearly state any assumptions you make about type of rootkit or delivery if necessary.
There is a bit of logging in the incomplete framework. Run
tail /var/log/syslog to display the last few lines of the syslog. You may also want to try tail -f /var/log/syslog to interactively tail the syslog file. In interactive mode as new lines are printed to the log your terminal will update immediately. Press ctrl-c (that is ctrl and then c) to end the tail command and get back to the shell.
Part B - Backdoor (15 Marks)
-
5 Marks Write a new hook for the
execvesyscall using the framework code from Part A. Consult the execve man page to learn the details and function signature ofexecve(). You will need to know which__NR_Xdefine is used to find the offset insys_call_tableto hook forexecve(whereXwill vary syscall to syscall). You might find https://elixir.bootlin.com/linux/v5.4.171/source/arch/sh/include/uapi/asm/unistd_64.h useful in this regard.
The hook should print the name of all files being executed, and the effective UID of the user executing the file to syslog usingprintk. Example output:
Jan 28 20:49:17 COMP4108-A2 kernel: [81423.749198] Executing /usr/bin/tail Jan 28 20:49:17 COMP4108-A2 kernel: [81423.749200] Effective UID 0 Jan 28 20:49:19 COMP4108-A2 kernel: [81425.950497] Executing /bin/ls Jan 28 20:49:19 COMP4108-A2 kernel: [81425.950499] Effective UID 1000
Thecurrent_*macros defined in the https://elixir.bootlin.com/linux/v5.4.171/source/include/linux/cred.h include will help you get the information you need to include in yourprintkmessage.
Hint:
You may also find the syscall man page to be helpful with understanding how to access the arguments passed to the syscalls we are hooking. Using the commanduname -awe can find the corresponding argument registers for x86-64 by looking at the second table in the Architecture Calling Conventions section, and compare this to how theopenat()hook code is able to access thepathnameargument. -
10 Marks
Modify your hook code so that when the effective UID of the user executing an executable is equal to the value of the
root_uidparameter, they are given uid/euid 0 (i.e. root privs). Theroot_uidparameter must be provided via theinsmodcommand ininsert.sh. Note that theroot_uidparameter should be set to your user's UID to get root, not root's UID. You will need to add this behaviour.
Hint:In order to get full marks you must demonstrate the module working. Set the
The header file https://elixir.bootlin.com/linux/v5.4.171/source/include/linux/cred.h and the corresponding code in https://elixir.bootlin.com/linux/v5.4.171/source/kernel/cred.c are likely of interest. Specifically, theprepare_kernel_cred(), andcommit_creds()functions.
root_uidparam ininsert.shequal to your user's UID, and provide the input/output from:
- Building the module code
- Runing
whoamias a normal user in one terminal - Inserting the module as a root user by running
./insert.shin a second terminal. - In your normal user terminal running
whoamiagain and being told you are root.
comp4108@NodeX:/A2/code/rootkit_framework$ whoami comp4108 comp4108@NodeX:/A2/code/rootkit_framework$ whoami root
Remember:
Provide enough detail in your report to demonstrate that you understand the problem and solution.
SUBMITTING CODE WITHOUT EXPLANATION WILL RESULT IN SEVERE PENALTY!
Part C - File Cloaking (25 Marks)
ls and the OS provided directory abstraction.- 10 Marks Write a hook for the
getdents64system call (man page here). Once again this will require finding the__NR_*define for the syscall number.
You will want to familiarize yourself with the linux_dirent structure. Your hook code should print the name of all directory entries returned by a call togetdents64()to syslog usingprintk. Sample output:
Oct 1 11:44:36 COMP4108-A2 kernel: [ 2266.441674] getdents64() hook invoked. Oct 1 11:44:36 COMP4108-A2 kernel: [ 2266.441704] entry: rootkit.o Oct 1 11:44:36 COMP4108-A2 kernel: [ 2266.441706] entry: .rootkit.mod.o.cmd Oct 1 11:44:36 COMP4108-A2 kernel: [ 2266.441708] entry: .. Oct 1 11:44:36 COMP4108-A2 kernel: [ 2266.441710] entry: insert.sh Oct 1 11:44:36 COMP4108-A2 kernel: [ 2266.441711] entry: rootkit.c Oct 1 11:44:36 COMP4108-A2 kernel: [ 2266.441712] entry: rootkit.mod.c Oct 1 11:44:36 COMP4108-A2 kernel: [ 2266.441714] entry: rootkit.ko <snipped>
-
15 Marks
Modify your hook such that the
struct linux_dirent*buffer you return to the calling process does not include any dirents for filenames that start withmagic_prefix. Themagic_prefixcharacter array should be provided as a kernel module parameter given toinsmodin theinsert.shscript. You will need to implement this parameter yourself.
After coding yourgetdents64hook and implementing themagic_prefixparameter you'll want to test it in action:- Edit the
insert.shscript and set themagic_prefixparameter to$sys$ - Compile your module by running
make - Create a file called
$sys$_lol_hidden.txtin your current directory. - Perform a
ls -lto see if your$sys$_lol_hidden.txtfile was created. - Insert the kernel module by running the insert script
./insert.shas root. - Run the same
ls -lcommand to validate the$sys$_lol_hidden.txtfile is no longer included. It shouldn't be inls -laeither (i.e. isn't just a regular 'hidden' dotfile).
Hint:Example output (from normal user term):
If you use$sys$as yourmagic_prefixvalue you must remember to escape the$s in the bash shell. The easiest way is to use\$instead of$when trying to create, edit, delete, or otherwise interact with one of your hidden files.
comp4108@COMP4108-A2:/A2/code/rootkit_framework/test$ touch \$sys\$_lol_hidden.txt comp4108@COMP4108-A2:/A2/code/rootkit_framework/test$ ls -la total 8 -rw-rw-r-- 1 comp4108 comp4108 0 Oct 1 11:59 bar.txt -rw-rw-r-- 1 comp4108 comp4108 0 Oct 1 11:59 baz.txt -rw-rw-r-- 1 comp4108 comp4108 0 Oct 1 11:59 foo.txt -rw-rw-r-- 1 comp4108 comp4108 0 Oct 1 12:00 $sys$_lol_hidden.txt comp4108@COMP4108-A2:/A2/code/rootkit_framework/test$ ls -la total 8 drwxrwxr-x 2 comp4108 comp4108 4096 Oct 1 12:00 . drwxrwxr-x 5 comp4108 comp4108 4096 Oct 1 11:59 .. -rw-rw-r-- 1 comp4108 comp4108 0 Oct 1 11:59 bar.txt -rw-rw-r-- 1 comp4108 comp4108 0 Oct 1 11:59 baz.txt -rw-rw-r-- 1 comp4108 comp4108 0 Oct 1 11:59 foo.txt
Hint:
 Modifying the buffer of
Modifying the buffer of dirents to hide files is the trickiest bit of the assignment. Luckily it is no more difficult than a typical data structure question (with a few twists).
Your objective is to sanitize thestruct linux_dirent *dirpbuffer provided as the 2nd argument to thegetdentssyscall. This buffer is allocated by the calling process (i.e they make sure there is enough memorymalloc'd for thestruct linux_dirents that the syscall puts into the buffer.)
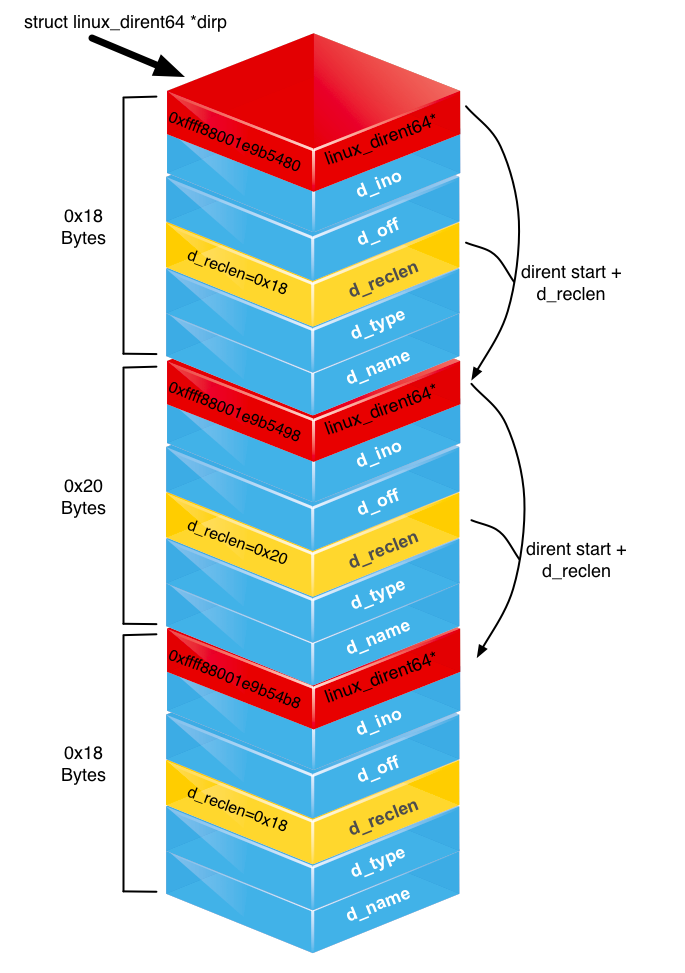
The most important thing to know is that thedirpbuffer is not an array ofstruct linux_dirents of equal size. To save memory eachdirentstruct is only as big as it needs to be. In order to allow iterating through thedirentstructs in the buffer eachdirentstruct stores its length to be used as an offset to the nextdirentin the buffer (see the figure). You will need to use this knowledge to determine how you can remove adirentfrom the buffer. The man page forgetdents()has example code for iterating the buffer.
The second most important thing to know is that thedirpbuffer is userland memory You can not edit it directly or bad things will happen. Instead you must first allocate a kernel memory buffer of equivalent size. To do this you must usekallocandkfreenot their user-land counterpartsmallocandfree. Once you have a kernel buffer of the right size you can use thecopy_from_userandcopy_to_userfunctions to copy the userland buffer into your kernel buffer and vice versa.
So, the steps are:
- Call the original
getdents64()syscall with thedirpbuffer your hook receives to have it populated withdirentstructs. - Allocate a kernel buffer of the correct size using
kmalloc - Copy the userland buffer into your kernel buffer using
copy_from_user - Perform your edits on the kernel buffer to remove any
direntstructs you don't want seen. - Copy your edited kernel buffer into the userland buffer with
copy_to_user - Call
kfree()on the kernel buffer to free it and avoid a leak.
Remember:
Provide enough detail in your report to demonstrate that you understand the problem and solution.
SUBMITTING CODE WITHOUT EXPLANATION WILL RESULT IN SEVERE PENALTY! - Edit the